
Demystifying the Dark Web and DarkNets, Part IV
Corporate Spies, Scammers, Spammers, Stalkers, and Cyber Criminals
Author: Anonymous Hacker, as told to Lindsey Watts
Preface:
Thus far in our series, we’ve looked at what DarkNet types exist in addition to the dark web, communication methodologies on DarkNets, social-ethical questions raised by anonymous, and unregulated and un-censored communication platforms. Your interest might be piqued at this point but if not hold onto your seat because it’s about to be.
In the event you decide to explore DarkNets on your own in the future, our anonymous source wants to make sure you know what you’re getting into. Hacking communities are not known for being easy to navigate, so consider this week’s installment as a sort of “hacker communities for dummies”.
(…raises hand in self-awareness…)
Most of what we “muggles” know about hacking comes from movies, news articles, and that 20-something down the block who still lives in their mom’s basement. We hear terms like threat actors, cyber criminals, and hackers, but there are many other categories and subcategories within the hacking community, as it turns out. Within those groups, there is also a wide array of intentions for being on DarkNets, as well as varying skill levels.
Now, let’s get to the good part. This week, we begin our introduction to a whole cast of DarkNet characters, covering four types of hackers and how they use malicious channels.
Corporate Spies
We typically think of corporate spies as people who steal competitive IP or customer data from a competitor. However, in this context we are talking about people with access to sensitive corporate assets who are actually willing to open the door for cyber attackers in exchange for payment. The way this works is that a user will share their access credentials with a malicious hacker, and the hacker will use these legitimate credentials to get inside the network and perform reconnaissance. It’s highly unlikely the attacker will use these credentials to actually attack the network, because they don’t want to give away their source. If they burn that person in the process, they might lose future access to the account or compromise their reputation in DarkNet circles. If an attacker is known for exposing the credentials of their paid corporate spies, they won’t likely secure more in the future. Once attackers have either navigated laterally to someone else’s account, or built another attack method, they execute the attack, and leaving the spy’s credentials out of their plan entirely from that point on. The spy gets paid, their company gets compromised, and everyone goes on their way.
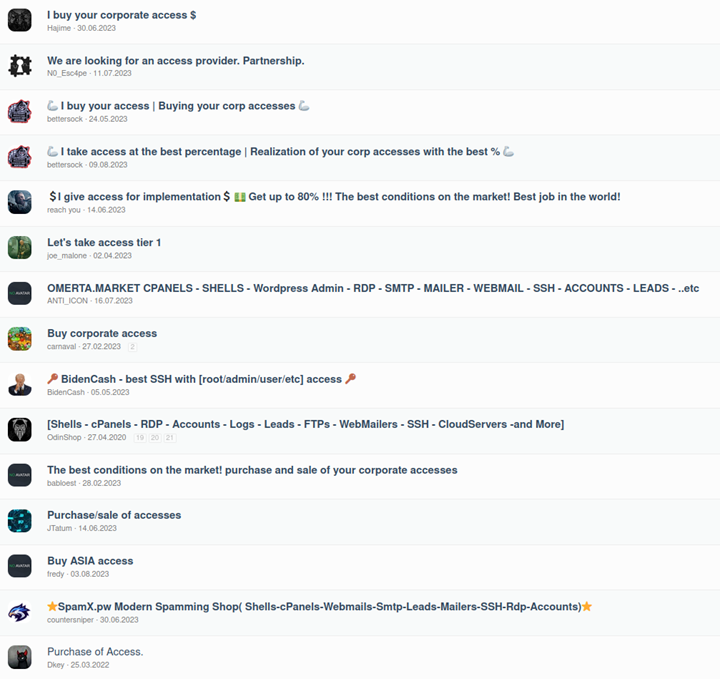
In this DarkNet screenshot, cyber stalkers advertise their services for sale.
In a simpler scenario, a corporate spy could also be someone who has left your company and uses their old credentials to gather and feed company information to their new employer. This is still considered hacking – whether or not it ends up on a DarkNet, and it’s the reason corporate IT and HR teams own the collective responsibility of cutting off all company access when an employee leaves for any reason.
Scammers
The same way one might run into local scammers in a seedy billiards bar or casino, DarkNets are also rife with people running their own games. The difference is that an experienced scammer doesn’t come to you; they draw you to them.
Scammer Type I: The sad truth is that many people go to DarkNets not for the chance to interact digitally as an anonymous user, but to look for illegal goods or services anonymously. As new DarkNet users (or as experienced hackers call them – “n00bs”), these people may have bad intent, but they also don’t yet know who they can trust to deliver. In a sense, it’s probably karma that these buyers end up in the hands of scammers, but there is definitely no shortage of people who will gladly accept money for goods or services they have no intention of delivering.
More likely than not, this kind of buyer is impatient and not a repeat customer, making them rife for exploitation (that they probably deserve). Services someone might seek on a DarkNet might include bringing harm to another person, having an ex-partner stalked, or worse. So, they come to a DarkNet with money in hand, looking to do harm, and criminals are more than happy to take their money without ever having to deliver a thing. Further, scammers are likely to keep a full record of the request for future blackmail purposes, so anyone hunting for illegal services could potentially be scammed on multiple layers.
Scammer Type II: More commonly, people are looking to execute scams on unknowing people on the clear net, through email schemes, falsified websites, and any other way money can be collected. These scammers have to be highly committed to what they’re doing, because once detected, their cover is blown permanently. They will be added to every known signature list through threat intelligence feeds and will only be able to successfully pull off the same scams on very uninformed people groups. This is why it’s so important to protect vulnerable people using social media or other internet-facing services. Scammers can certainly be found on DarkNets, but most career hackers see themselves as above such operations.
“Scammer” Type III (Stings): Another scenario that is important but might feel like a “scam” to the buyer is seller impersonation. Since law enforcement agencies also employ hackers to intentionally frequent DarkNets in search of illegal activity, there is always a great chance that a buyer could accidentally entrap themselves and end up in jail. Again, karma. This is the good kind of “scam” according to most people, because it interjects accountability into a world of anonymity. It’s one way to limit exploitation of good people without shutting down uncensored forums and marketplaces.
Spammers
We typically think of these unwanted irritants as advertisers who text us ads, submit repeated solicitation forms on our websites, or execute mass email campaigns with one goal – to make money. However, since DarkNets are just a reflection of our existing world, when people see that a tactic might return 10% profit at their day jobs, they are going to transfer that knowledge to endeavors on the DarkNet for side-gigs that are less than legal. Spammers on DarkNets may gain access to a channel or forum, only to post and send obnoxious messages to other members advertising their services. While experienced users (black hats, some white hats, and cyber warriors) know what to avoid, new users (“newbies” or “n00bs”) may get excited and open their wallets.
Stalkers
These worrisome people often target celebrities, but stalkers may target anyone, for any reason. This type of hacker is unique because all their hacks and tricks are designed to be targeted toward an individual, and they are for hire.
Up to 13% of males and up to 32% of females will experience stalking of one form or another at some point in their lives. Psychology Today categorizes stalkers into three types: people who feel rejected, those who seek intimacy, and those who feel resentful. This could include disgruntled family members, ex partners, would-be lovers, fans, hitmen, bounty hunters, and even governments looking to track down an individual.
In cyber stalking there are typically at least two people working together – the person who wants to stalk (customer) and the person who provides a service (the cyber stalker). [Note – these could certainly be one and the same for anyone who manages to pique the interest of a capable hacker who lacks a moral compass.]
Skilled cyber stalkers can start with as little as one easily obtained piece of personal information relating to the target, such as a gaming name, email address, full name, etc. to find out the target’s full identity, home address, mobile number, etc. Their GPS signals can also be hacked and traced through cell phones, vehicles, Fitbits, smart watches, etc., and they can be tracked by the WiFi they use to connect to the internet for weeks or months at a time. Then, their daily, weekly, and monthly schedules can be mapped out alongside travel routes, purchases, and more. This can also be combined with information available through data leaks on DarkNets that contain SSN, alternate email accounts, bank accounts, and more.
When the Equifax hack happened, it opened many people’s eyes to the dangers of web applications and internet-facing companies that collect, store, and process personal information. The danger is far beyond credit monitoring when contextualized this way. Those SSNs can be connected with other caches of health information collected during malicious data exfiltration campaigns. How do they find this information? Remember the letter you got from your doctor notifying you that their systems had been compromised? (Most people we know have received at least one of these notifications from some health, banking, or other organization that was breached, exposing personal data.) Just because no one tried to use your credit card or SSN to create a false identity, that doesn’t mean you are in the clear. If one database has some of your information, and another has more, those pieces can be assembled at any point to paint a clear and terrifyingly accurate picture of any of us – our lives, our families, etc.
We’ve all heard the stories of people having their baby monitors or home appliances hacked, and more recently, it was discovered that smart lightbulbs have been used to hack into home networks – that would definitely qualify as stalking, as well. Most people choose to believe that no one would want to bother with them, but it’s hard to know when someone will suddenly decide to target you. The threat of being stalked at some point in the future is enough to make one question the purchase of internet connected cars, smart watches, and IoT-connected home devices.
Cyber Criminals
Contrary to popular belief, cyber criminal is not a blanket term for all people who commit cyber attacks. This is the term many news sites use, so it’s a common misnomer. Rather, cyber criminals are like junior hackers. They are willing to do bad things and have figured out how to navigate DarkNets, but they haven’t yet proven themselves as capable and trustworthy. So, an organized hacking group like a FIN or APT won’t accept them as a paid member until they “earn their stripes”.
Here, we can apply the psychology of an ambitious intern to the world of digital crime. They may be anxious to learn and prove their skills, making them a bit dangerous to potential victims for their willingness, but they are equally as dangerous to themselves for their lack of knowledge and skill. Still in the learning phase of how to navigate anonymously, they could easily get caught hacking – which is exactly why larger groups won’t touch them yet.
[NOTE: Cyber criminals are people who want to build a cyber career and may have some skill, but are still unworthy for any major criminal undertakings with organized groups. If they become skilled, but fail to get hired as criminals, they may eventually become dangerous rogues – covered in the next installment]
If you would like to speak with an expert about testing your incident response plan to make sure you don’t have any gaps that could lead to failure during a real cyber attack, you can reach out to us here anytime. We have the right people on hand to help.