Brute Forcing a Login Page with Burp Suite
By: Steven Anderson, Senior Security Consultant at CISO Global
What Tools Are Used in a Penetration Test?
When we talk about penetration testing, or “pen testing”, what exactly do we mean? Penetration testing is an exercise that demonstrates risk, simulates a malicious attack, and gains an enhanced understanding of an IT environment. The test might include guessing passwords, scanning ports, or conducting a purple team exercise.
It sounds complicated. And it can be. But there are a multitude of tools that make this job easier. One such tool is Burp Suite. Professional security researchers and bounty hunters use this modular toolset to conduct system tests. Burp Suite is classified as an Interception Proxy, or server capable of performing Man-In-the-Middle attacks. Using Burp Suite’s Intercept capability, a pen tester can interrupt a connection between an end-user or device and the internet or target server. This allows the pen tester to get a better understanding of what the target server expects in a web request, collect sensitive information the end user provides, and modify requests or responses to manipulate the end user or server into divulging sensitive data or providing access.
Brute Force Using Burp Suite
Pentesters perform numerous types of attacks during a penetration test, including exploiting existing vulnerabilities, leveraging open/insecure services/protocols, and abusing weaknesses in access controls. In this blog, we’ll look at another type of pen testing attack: brute forcing a log in page. A brute force attack employs guessing an unknown variable repeatedly. The guesswork employed may use random words/strings or may involve a more targeted approach using existing knowledge of the target software, system, company, or person. Brute force attacks are not restricted to usernames and passwords such as demonstrated in this blog. There are several well-known open-source brute force tools, such as Hydra and Ncrack, that are great for brute-forcing access over many protocols such as SSH and RDP. We selected Burp Suite for this demonstration because it is more suitable for brute forcing a web application login page. (It should be noted here that this and other pen testing tools are also hacker tools. We use the same tools and techniques attackers use to provide the most accurate results as to how secure your environment truly is.)
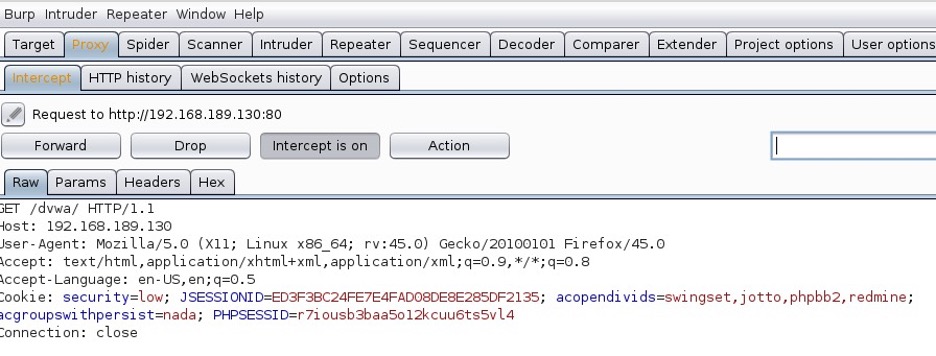
Setting Burp Suite as a Web Proxy
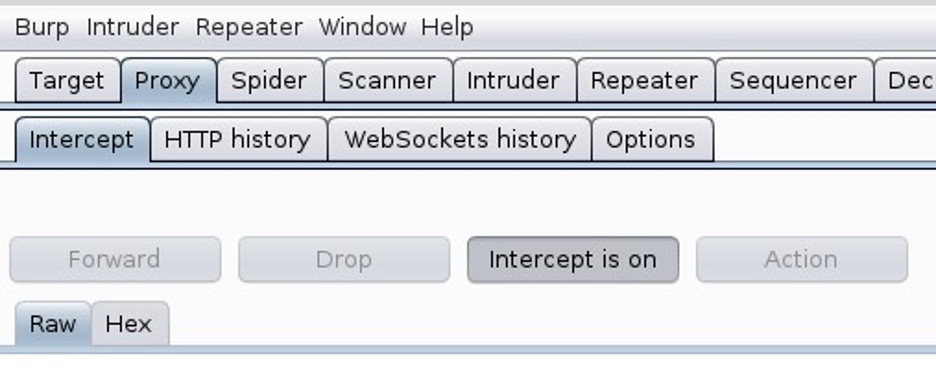
Burp is designed to be used alongside your browser. It functions as an HTTP proxy server, and all your HTTP/S traffic from your browser passes through Burp. To ensure that Burp’s proxy listener is working, select the Proxy tab and make sure that you see the Intercept is on optionis not greyed out, as shown in Figure 1.
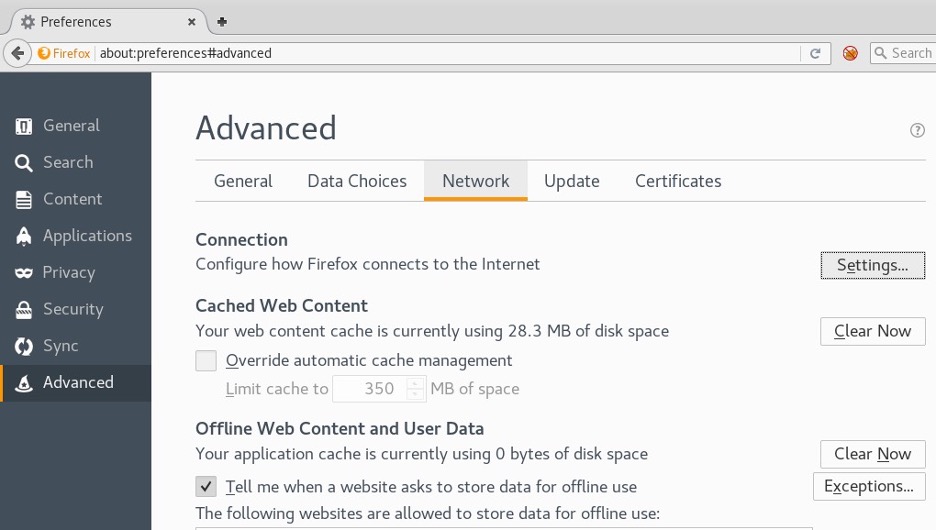
Next, configure your browser to use Burp Proxy listener as its HTTP proxy server. To do this, change your browser’s proxy settings to use the proxy host address (127.0.0.1) and port 8080 for both HTTP and HTTPS protocols. In this demo, Burp Suite is being run in Kali. Firefox is the default browser in Kali, so open Firefox and go to Preferences. Click Advanced, select the Network tab, and click Settings, as shown in Figure 2.
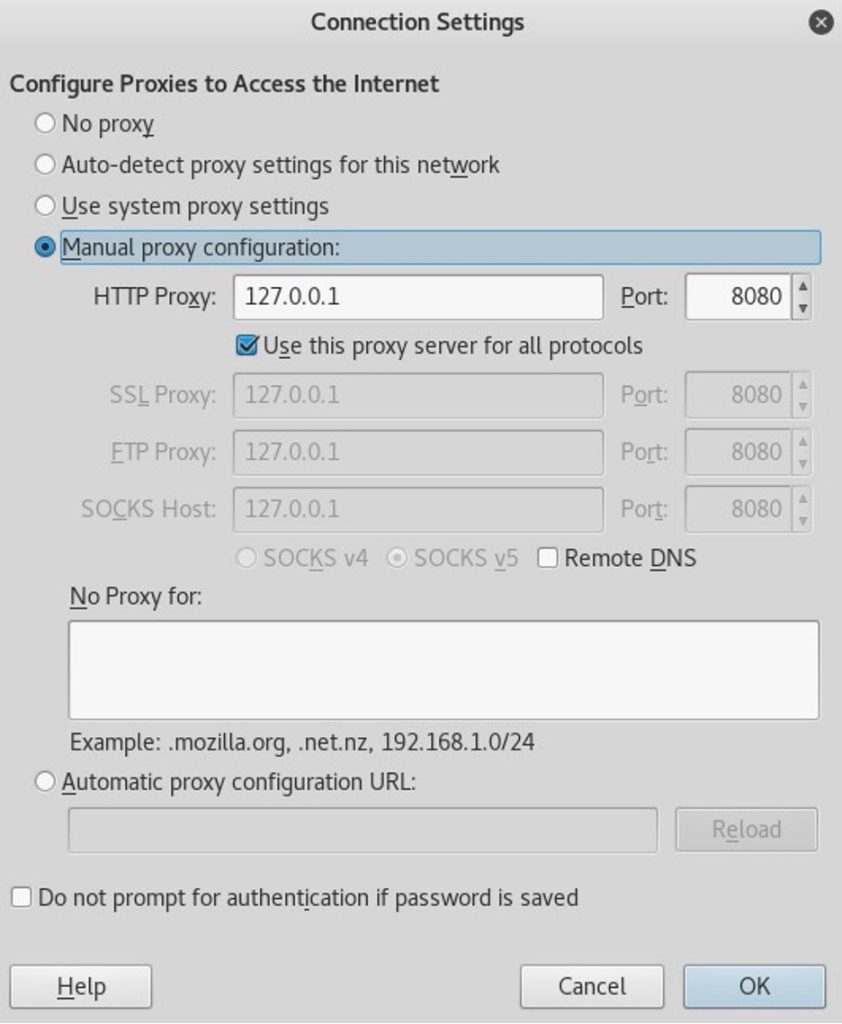
Select the Manual proxy configuration radio button. Enter 127.0.0.1 in the HTTP Proxy field and enter 8080 in the Port field. Make sure the Use this proxy server for all protocols box is checked. Delete anything that’s in the No proxy for: field. Select OK to save the settings (see Figure 3).
Now, if everything is configured properly, all your HTTP/S traffic should go through Burp. Whenever you visit a website, the Proxy tab in Burp will change its color to orange, and Burp will hold on to the request until you decide what to do with it. At this point, you can turn off the intercept and only turn it on when you need it (see Figure 4).
How to Brute Force a Login Page
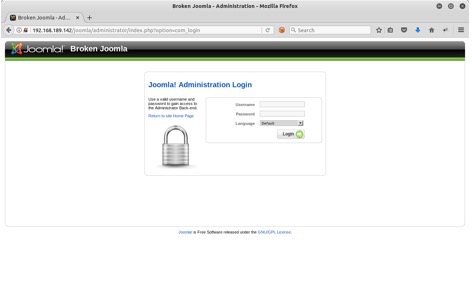
Let’s say you are performing a penetration test against your client’s website, and you come across a Joomla! administrator interface. If you can brute force the admin account, you will have total control over the website. To brute force the login page, open Burp and make sure Burp’s intercept is on (see Figure 5).
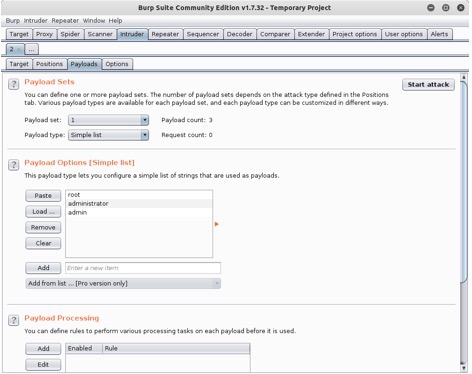
In this demonstration, we will brute force both the username and password. If you are unfamiliar with the installation you are attacking, you may find it useful to use existing username/password lists (in Kali, you can find these in /usr/share/wordlists). In this case, I made my own username list because I am certain that the username would be one of these three: root, administrator, or admin (see Figure 6).

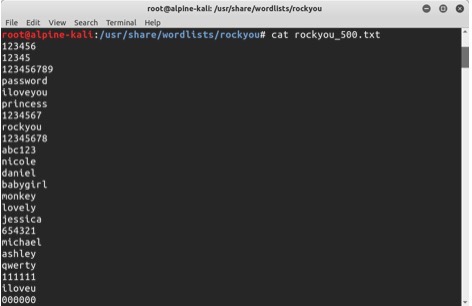
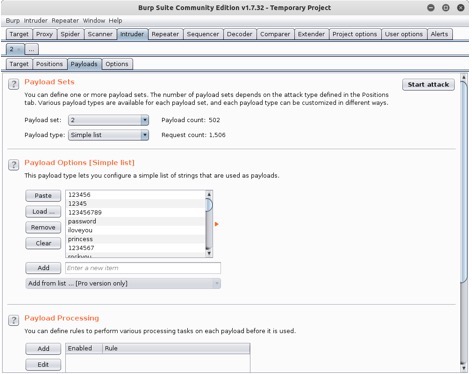
For the password list, I chose to use the top 500 passwords from the rockyou password list (see Figure 7).
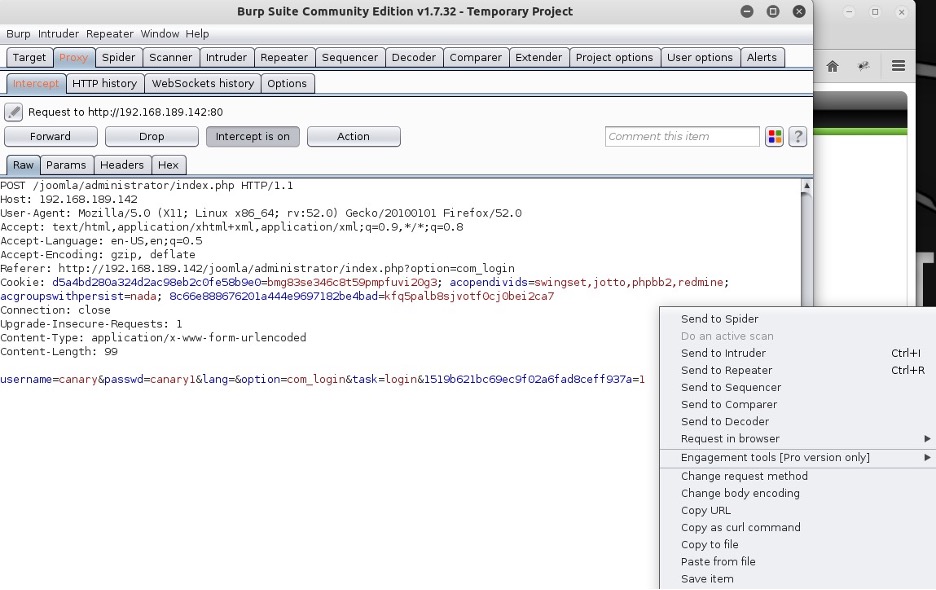
Once you have your username and password lists ready, type anything in the username and password fields; I am using canary/canary1. Burp will capture your HTTP request, and it will be waiting for your action. You’ll be able to see what you’ve put for the username and password, as shown in Figure 8. Right-click and select Send to Intruder. Click Drop, and deselect Intercept is on.
Click the Intruder tab, and click the Positions tab, as shown in Figure 9. Make sure the Attack type is set to Cluster bomb from the drop down menu (if you already know the username and only want to brute force the password, select Sniper). Burp highlights all the positions where payloads can be inserted. We are only interested in username and passwd parameters. Select Clear and highlight canary and click Add. Do the same thing for canary1.

Go to the Payloads tab and click the Payload set drop down menu. You can see that there are two payloads: one for the username and one for the password. Choose 1 and click Load to load the username list (see Figure 10).
Do the same thing for password after you select 2 in the Payload set field. Now, launch the brute force attack by clicking Start attack at the top right corner (see Figure 11).
While Burp is brute forcing the login page, check any anomalies in the responses (see Figure 12).
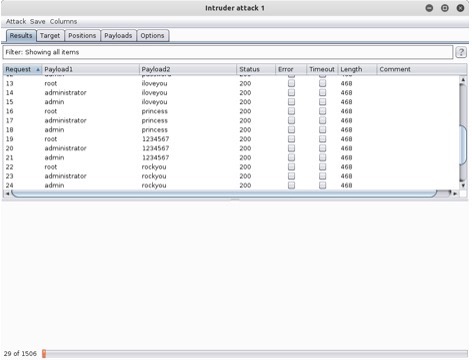
Going through the requests, I noticed that the status for the request 78 is 301 (see Figure 13). All the other requests came back with a 200, displaying “Username and password do not match.” This lets me know that this entry is the username.
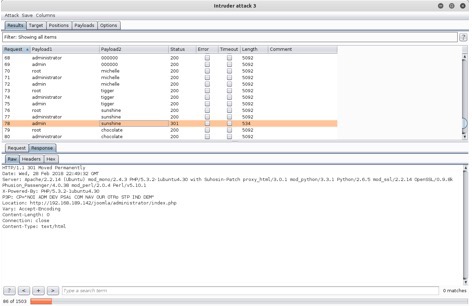
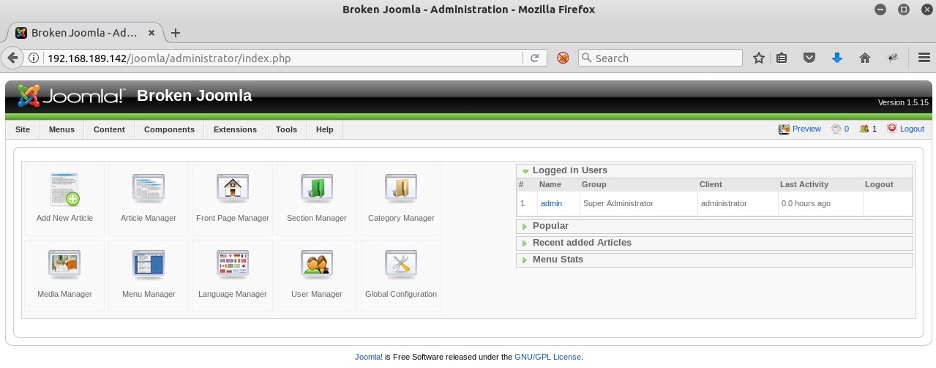
I entered the username and password used by request 78 (admin/sunshine) and was able to get into the administrator interface (see Figure 14)! Attack complete!
As this demonstration shows, a brute force attack is trivial to perform. However, you can take a couple of steps to reduce the chances of succumbing to a successful brute force attack:
- Use complex passwords. The more complex the password, the more difficult it is to guess/brute force. Consider requiring staff to set passwords that are lengthy and include lowercase and uppercase letters, numbers, and special characters.
- Set login delays or account lockout policies for all login interfaces. It is extremely difficult to brute force an account when the account locks after five unsuccessful password-entry attempts or requires you to wait 10 minutes before trying to enter your password again.
Using the Right Tools and the Right Team
Penetration testing employs many techniques and tools to identify potential vulnerabilities and exploits in your network, such as easily hackable passwords— using Burp Suite is just one of them.
Solutions such as Endpoint Protection are more than just a set of tools. The right tools, the right intelligence, and the right team can help protect and secure your endpoints to keep your data safe from cybercriminals and malicious actors, preventing crippling disruptions and expensive setbacks while avoiding hidden costs.
Contact us to discuss your security needs and discover more about how Cerberus Sentinel can help you improve your security posture.