CMMC 2.0: Your Questions Answered
By: Tom Cupples, Ed.D., CISSP, CGRC, PMP, CAICO-PI, CCP, CCA, Sec+, Net+, Security Controls Assessor & Senior Cybersecurity Trainer at CISO Global, Inc.
By now, you are likely aware that the Cybersecurity Maturity Model Certification (CMMC) Program Proposed Rule was published in the Federal Register on December 26, 2023. This set into motion a series of deadlines, which will culminate in the full implementation of CMMC 2.0. It also set into motion a flurry of activity within the Defense Industrial Base (DIB) and the realization that a deadline for compliance looms large. This article will address some of the questions about CMMC, its requirements, and its effect on the participants of the DIB.
What is CMMC, and How Did It Originate?
CMMC has evolved out of several codes and regulations. Ultimately, the seed was planted with Presidential Executive Order 13556 in 2010, which sought to provide standard protection for the processing, storing, and transmitting Controlled Unclassified Information (CUI). It also set forth a definition of CUI.
The Department of Defense (DoD) first announced the CMMC framework in 2019. In 2020, the DoD released the first iteration of the framework. This framework consisted of five progressively more mature cyber hygiene levels: Level 1 – Basic Cyber Hygiene, Level 2 – Intermediate Cyber Hygiene, Level 3 – Good Cyber Hygiene, Level 4 – Proactive Cyber Hygiene, and Level 5 – Advanced or Progressive Cyber Hygiene.
The DoD announced the “new and improved” CMMC 2.0 in 2021. Its purpose is to simplify and demystify the framework and, therefore, reduce the cost of implementation. It collapses the framework into three levels: Level 1 – Foundational, Level 2 – Advanced, and Level 3 – Expert.
What Sets CMMC 2.0 Apart from CMMC 1.0?
The transition from the original CMMC framework to CMMC 2.0 represents a significant shift in the DIB’s approach to cybersecurity compliance. The benefits of transition are a focus on simplification and accessibility. First, simplifying and redefining the levels will make it easier for practitioners to meet the challenge. Next, making certification more accessible to small businesses with the possibility of self-attestation will allow a smoother transition for small businesses.
However, one must not confuse simplification and accessibility with reduced accountability. Self-attestation does not relieve the organization or its leadership of regulatory accountability. The False Claims Act governs a false statement in an attestation. A CMMC Third-Party Assessment Organization (C3PAO) is required for those who wish to bid for and receive contracts that require Level 2 certification. It is recommended for those who wish to bid for and receive contracts that require Level 1 certification. Additionally, some prime contractors may require their sub-contractors to obtain the services of a C3PAO even at Level 1.
What are the Requirements of CMMC 2.0?
Referring to the Infographic below, you will notice the streamlining of the three levels of CMMC 2.0: Foundational, Advanced, and Expert.
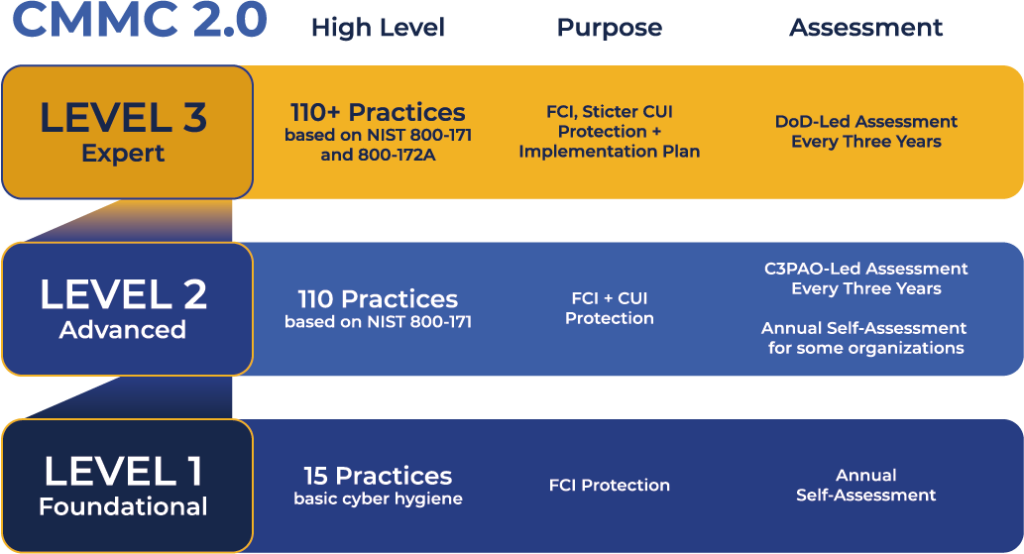
Level 1 (Foundational), or the original “basic cyber hygiene,” requires the implementation of 17 basic practices, is designed to protect the processing, storing, and transmitting of Federal Contract Information (FCI), and is self-attested annually.
Level 2 (Advanced) requires the implementation of 110 practices based on the NIST SP 800-171 revision 2, is designed to protect the processing, storing, and transmitting of FCI and Controlled Unclassified Information (CUI) and is assessed triennially by a C3PAO. (In a few special circumstances determined by the DoD, some may be allowed to self-attest.)
Level 3 (Expert) requires the implementation of 110 practices based on the NIST SP 800-171 revision 2, plus some of the practices of NIST SP 800-172, is designed to protect the processing, storing, and transmitting of FCI and even stricter CUI plus an implementation plan, and is assessed triennially by the DoD exclusively.
How Does CMMC 2.0 Compliance Enhance Cybersecurity Within the DIB?
At its core, CMMC 2.0 compliance is about fortifying the defense sector against cyber threats through a structured, comprehensive approach. By closely aligning organizational practices with established cybersecurity standards found in NIST’s SP 800-171 Revision 2 and SP 800-172, CMMC 2.0 seeks to ensure that organizations meet regulatory requirements and adopt best practices that strengthen their cyber hygiene and resilience. This alignment focuses on the essential cybersecurity practices necessary to protect sensitive defense information effectively. CMMC 2.0 is a blueprint for building a robust cybersecurity posture within the DIB, safeguarding critical defense assets, and bolstering national security.
What Does the Assessment Process for CMMC 2.0 Compliance Entail?
Understanding the assessment process is critical for organizations embarking on CMMC 2.0 compliance. The process begins with self-assessment, allowing organizations to gauge adherence to the required cybersecurity practices for their target maturity level. This introspective examination provides valuable insights into the organization’s cybersecurity posture and identifies areas for improvement.
For higher levels of certification and specific contractual requirements, mandatory third-party assessments are conducted by C3PAOs accredited by the CyberAB, the approved DoD accreditation body. These assessments objectively assess an organization’s cybersecurity maturity, providing a credible certification that meets DoD scrutiny. Obtaining third-party certification demonstrates an organization’s commitment to cybersecurity excellence and establishes trust within the DIB.
Due to the cost associated with third-party assessments, completing a self-assessment is highly recommended. Organizations can better prepare themselves for compliance and minimize unnecessary expenses by resolving any issues before engaging a C3PAO.
How Should Organizations Prepare for CMMC 2.0 Compliance?
Preparation is key to navigating CMMC 2.0 compliance effectively. It begins with a comprehensive understanding of the framework’s requirements and the organization’s cybersecurity posture. Next, conducting a thorough self-assessment enables organizations to identify risks, vulnerabilities, and threats requiring new control implementations.
The next crucial step is developing a detailed CMMC Plan of Action and Milestones (POA&M). This plan outlines the actionable steps, timelines, and resources necessary to achieve compliance with the required maturity level. It serves as a roadmap for the organization, guiding it through the readiness process and ensuring a structured approach to cybersecurity enhancement.
For organizations with limited cybersecurity expertise in-house, seeking professional guidance from cybersecurity practitioners with CMMC expertise can provide valuable assistance in navigating the certification process. These experts can offer insights, best practices, and strategies for navigating the complexities of the framework, ensuring a smoother journey toward achieving and maintaining CMMC 2.0 compliance.
The most valuable practitioners are those certified by the CyberAB’s Cybersecurity Assessor and Instructor Certification Organization (CAICO) with the designations of CMMC Certified Assessor (CCA), CMMC Certified Professional (CCP), and Registered Practitioner (RP), stated in order of expertise and most rigorous training and examination.
How Does CMMC 2.0 Address Small Business Concerns?
One of the critical questions surrounding CMMC 2.0 compliance is how it accommodates the unique challenges faced by small businesses within the DIB. Recognizing small businesses’ crucial role in the DIB, CMMC 2.0 has been designed with scalability in mind. This scalability is evident in the streamlined framework, which reduces maturity levels and focuses on essential cybersecurity practices that are both attainable and sustainable for small businesses.
CMMC 2.0 also introduces the possibility of self-assessments for lower maturity level contract requirements, significantly reducing the financial and administrative burden on small businesses. This approach makes compliance more feasible and encourages a proactive cybersecurity stance among smaller businesses, fostering a more resilient and secure DIB.
What are the Key Challenges in Achieving CMMC 2.0 Compliance?
Achieving CMMC 2.0 compliance presents various challenges for organizations, ranging from resource allocation to navigating the complexities of cybersecurity requirements. One of the primary challenges is the need for a deep understanding of the CMMC 2.0 framework and its application to an organization’s specific operational context. This necessitates a comprehensive assessment of current cybersecurity practices and identifying gaps that need bridging to meet the desired maturity level.
Another significant challenge lies in implementing required cybersecurity controls, particularly for organizations in their early cybersecurity maturity stages. This includes establishing policies, procedures, and practices compliant with CMMC 2.0 and integrating them into daily operations. Maintaining compliance amid evolving cybersecurity threats and changing regulations also requires ongoing vigilance and adaptation, adding another layer of complexity to compliance efforts.
CMMC compliance relies heavily on the organization’s ability to properly document its policies, procedures, and practices. One way to prepare for certification is to ensure alignment and consistency. Assessors will expect the documentation to be thorough and accurately represent that alignment.
Are Resources Available to Support Organizations in CMMC 2.0 Compliance?
Navigating a path to CMMC 2.0 compliance is a formidable endeavor, but organizations should not engage in this challenge in isolation. A wealth of resources is available to support organizations through every step of the compliance process. The DoD and the CyberAB offer comprehensive guidance, including official documentation, FAQs, and webinars to demystify the framework and its requirements.
In addition to official resources, a growing ecosystem of CMMC-certified experts and training providers has emerged, offering tailored support services ranging from gap assessments to compliance strategy development. Experts can provide invaluable insights and assistance, particularly for organizations seeking to navigate the more complex aspects of the framework or aiming for higher maturity levels. Training providers can educate an organization’s personnel assets on the framework, better preparing them to identify and implement the controls required by the CMMC framework.
Industry associations and peer networks also present collaboration and knowledge-sharing opportunities, allowing organizations to learn from their counterparts’ experiences and best practices. By leveraging these resources, businesses can enhance their understanding of CMMC 2.0, streamline compliance efforts, and strengthen their cybersecurity posture.
How Quickly Can My Organization Become Certified?
Considering the number of C3PAOs, CCAs, and CCPs available to assist in CMMC implementation is paramount. Some experts anticipate approximately 80,000 organizations will be required to obtain Level 2 compliance, yet only about 650 CCPs are available, 175 of which are CCAs. There are only 50 C3PAOs. This drastic difference in supply and demand will make it much more difficult to obtain an assessment as the window begins to close on the approach to full implementation of CMMC 2.0.
To this end, the DoD has implemented the Joint Surveillance Voluntary Assessment (JSVA) Program. This program allows organizations to voluntarily seek certification before CMMC goes into effect. Any organization certified under the JSVA will automatically satisfy CMMC’s requirements when it goes into full effect. Proactively seeking compliance sooner rather than later will improve the likelihood of becoming certified.
What Does the Future Hold for the DIB with CMMC 2.0 Compliance?
As organizations seek CMMC 2.0 compliance, the future promises a more secure and resilient DIB. The phased rollout and implementation of CMMC 2.0 signifies a commitment to strengthening cybersecurity practices across the DIB while allowing organizations time to become certified. CMMC 2.0 compliance takes time and effort. Current trends suggest that the later an organization starts working toward certification, the longer the queue becomes. Staying informed and proactive is essential as the landscape of CMMC 2.0 continues to evolve. Organizations can successfully meet current and future cybersecurity challenges by staying abreast of updates, engaging with industry resources, and fostering collaboration within the defense community.
CMMC 2.0 represents a pivotal step towards enhancing cybersecurity within the DIB. By embracing the framework’s requirements, organizations strengthen their cyber defenses, protect sensitive defense information, and contribute to national security efforts. With strategic planning, thorough preparation, and a commitment to excellence, organizations can navigate the complexities of CMMC 2.0, ensuring a secure and resilient future for the DIB and the nation.
I’m not a Member of the DIB. How can I get involved?
Individuals and organizations are needed to close the gap between those DIB participants and certified individuals and organizations available to meet the needs of the CMMC ecosystem. Experienced individuals interested in becoming certified to perform assessments in the ecosystem must first engage with a Licensed Training Provider (LTP) approved by the CAICO to conduct training. Training with an LTP is mandatory before taking the official examinations to become CCAs and CCPs. Experienced organizations interested in becoming C3PAOs must meet the same standards as those DIB members required to certify at CMMC Level 2 and become certified by the Defense Contract Management Agency (DCMA) Defense Industrial Base Cybersecurity Assessment Center (DIBCAC). Both individuals and organizations must first apply with the CyberAB.
Learn how CISO Global can help you on the journey to CMMC 2.0 compliance.